Here are my quick notes from the OWASP BeNeLux Days 2016 (#owaspbnl16) training day on threat modeling presented by Sebastien Deleersnyder. All the training slides can be found  here.
here.
Definition of threat modeling: activity of identifying and managing application threats. Threat Modeling should be ideally done on requirements phase of the project. The goal of threat modeling is to uncover flaws in the design of different features.
Threat modeling stages:
- diagram
- usually the Data Flow Diagrams are used.
- different diagram layers
- context diagram – very high level; entire component
- level 1 diagram – high level, one per feature
- level 2 diagram – detailed sub-components
- identify threats
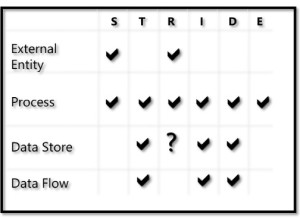
- identification can be done using the STRIDE Threat Model
- rank the threats by risk, to be sure that you are focus on mitigating the most important ones.
- how the STRIDE elements are applied to each element of the Data flow Diagram:
- mitigate the threats
- mitigation advice : keep it simple and do not reinvent the wheel.
- leverage proven best practices
- validate
- does the diagram match final code ?
- is each threat mitigated ?
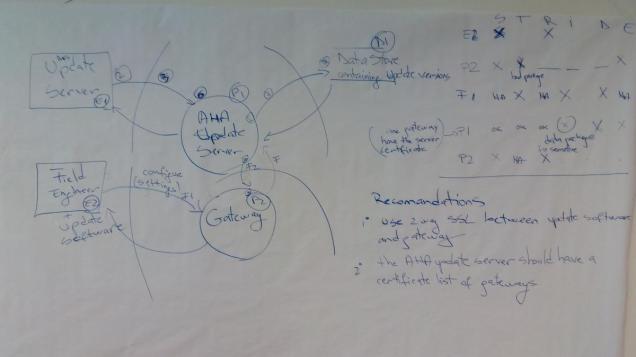
The training also had some hands-on exercises. I just upload here the last exercise representing the STRIDE analysis of an Internet of Things (IoT) deployment:
Some tools that can be used to help:
- whiteboards 🙂
- Microsoft Threat Modeling tool (free)
- Mind-Mapping diagram tools
-
MyAppSecurity ThreatModeler (commercial)
For me the training was a very good introduction to threat modeling and contained a lot of “from the tranches” tips and advices.
You must be logged in to post a comment.