Here are my quick notes from the BruCO N 2018 conference.This first day was called “Retro Day” because it contained the best (as chosen by peoples) previous talks. All the slides of the conference can be found here.
N 2018 conference.This first day was called “Retro Day” because it contained the best (as chosen by peoples) previous talks. All the slides of the conference can be found here.
Advanced WiFi Attacks using Commodity Hardware (by Mathy Vanhoef)
Wifi devices assume that each device is behaving fairy,share the bandwidth with the other devices for example.
With special hardware it is possible to modify this behavior ; It is possible to do:
- continous jamming; channel unusable.
- selective jamming; block specific packets.
Implementing of selfish behavior using cheap devices
Steps to send a frame:
frame1 + SIFS + AIFSN + backoff + frame2
- SIFS : represents the time to let the hardware process the frame.
- Backoff : random amount of time, used to avoid collisions.
Implement the selfish behavior (this was done by modifying the firmware):
- disable Backoff.
- reduce AIFSN.
Countermeasures to this problem:
- DOMINO defense system detects selfish devices
What if are multiple selfish stations ?
in theory : in collision both frames are lost but in reality due to the “capture effect” in a collision the frame with best signal and lowest
bit-rate is decoded (similar to FM radio).
Continuous jamming
how it works:
- instant transmit:disable carrier sense
- no interruptions : queue infinite packets
This will
– only first package visible in monitor mode
– other devices are silcenced
What is the impact in practice:
We can jam any device that use the 2.4 and 5 GHz band, not only wifi, but other devices like security cameras.
Selective jammer
Decides based on the header whether the jam the frame
so it should:
- detect and decode the header.
- abort receiving current frame.
- inject dummy packet
The hard part is the first step. This is done by monitoring the (RAM) memory written by the radio chip.
Impact of the attacks on higher layers
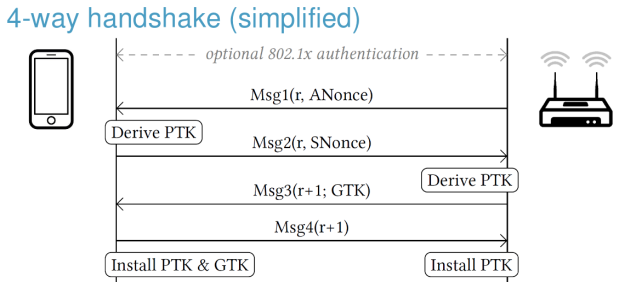
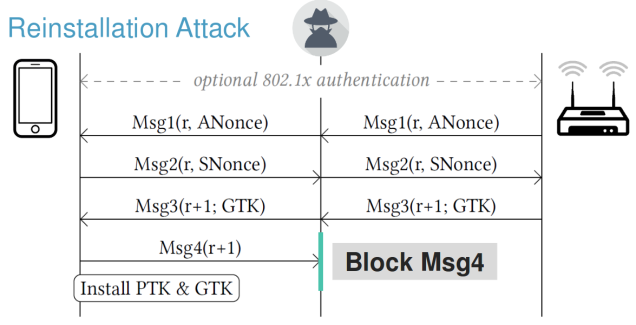
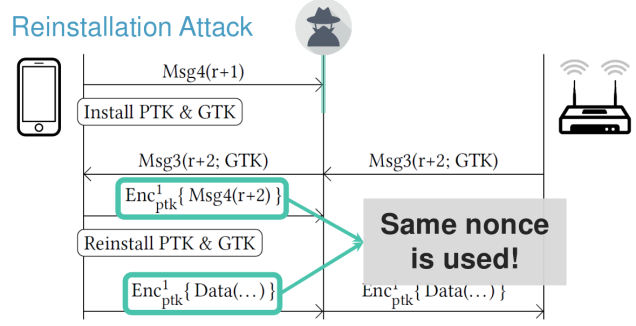
Breaking WPA2; this is a shorter version of :KRACKing WPA2 in Practice Using Key Reinstallation Attacks.
Hacking driverless vehicles (by Zoz)
Drivelless vehicles advantages:
- energy efficiency
- time efficiency
Main roadblocks:
– shared infrastructure (have to share road/s with card driven by humans)
– acceptance (safety robustness).
Classical failures:
- RQ-3 DarkStar – self flying drone; it crashed due to cracks into the runway.
- sandstorm ; self driving car contest: in this case the mismatch between GPS info and other sensor.
Autonomous vehicle logic structure:
Mission task planners
|
Navigation
|
Collision avoidance
|
Control lops
Sensors used by driveless vehicles:
- active vs passive sensors
- common sensors:
- gps
- lidar
- cameras
- wave radar
- digiwheel encoderes
Sensor attacks
2 kinds:
- denial
- spoofing – craft false data
GPS:
- denial – jamming
- spoofing – fake GPS satellite signals
LIDAR
- denial:
- active overpowering
- preventing returning signal
- spoofing
- can fake road markings invisible to humans
- can make solid looking objects
Digital compass:
- extremely difficult to interfere with acoustic attacks.
- gyroscope vibrates and has a resonance frequency.
Levelling Up Security @ Riot Games (by Mark Hillick)
The talk was structured in 2 parts; what RiotGames do/did to enhance security in 2015 and what they are doing to enhance security in 2018
2015
- introduced the idea of security champion.
- introduced the RFC (Review For Commens) document = Technical Design.
- not an approval process it’s more about receiving advice
- becomes a standards through adoption.
- introduction of bug bounty program.
2018
- security team had doubled in size.
- sec-ops team and read team are working together.
- put in place an anti-cheating strategy:
- prevention
- detection
- deterence
Top8 vulnerabilities:
- improper authentication.
- open redirect.
- information disclosure.
- business error.
Challenges around secrets:
- detected an api key from AWS in a commit.
- how to fix it.
- provide temporary AWS API token
- remove the usage of long-lived AWS Api keys.
Social engineering for penetration testers (by Sharon Conheady)
Definition: efforts to influence popular attitudes and social behavior.
Main take away (for 2018); the social engineering (a.k.a SE) is used more and more and actually the techniques it didn’t change too much.
what has changed since 2009 ?
nothing
example of social enginnering through history:
- Spanish prisoner
- The letter from Jerusalem
- Nigerian scams (1980)
- Friend scams
What had changed since 2009 (when the same talk has been given):
- the scale of the attacks.
- sophistication
- more targeted
- ethical SE is mostly phishing.
Why social engineering (still) works:
- peoples want to help.
- greed
- tendency to trust
- complacency
- peoples do not like confrontations.
Stages of an attack
- target identification
- reconnaissance
- passive information gathering
- physical reconnaissance
- google map
- where are the security guards
- sample scenarios
- tailgate
- going in for the attack
- use your scenario to get in
- prove you were there
- have an exit strategy
- write the report
- tell the story
The 99c heart surgeon dilemma (by Stefan Friedli)
The presentation was about pen test bad examples and how to make the things better.
It starts with examples of bad pen test:
- Unclear impact metrics.
- Accidentally pasting other customer names.
- Reported false positives.
How to make the things better:
- Avoid security companies offering bad services. How:
- Ask about procedures, standards.
- Ask to talk to the testers
- Check for community participation
- Look at sample deliverables
- How to fix Penetration Testing:
- Involve more people.
- Have more conversations.
- Don’t stop at the report

You must be logged in to post a comment.