Here are my quick notes from the BruCON 2017 conference. All the slides can be found here.
How hackers changed the security industry and how we need to keep changing it
Back in the ’90 the hacker community was looked with suspicion by the software industry because the hackers were finding security problems and the software publishers had no process to handle this findings.
Back in the 90’s the only reference in order to create a secure system was the “Orange book“; but the orange book it’s all about security features, no word about bugs or vulnerabilities.
CERT – internet community had no means to fight against malware that’s why CERT was created. But the hacker community do not participate to CERT anymore because there was no traceability of the issues reported, so the Bugtraq was created.
Hackers created the concept of pen-test and the first (hacking) tools :
- crack
- satan (first network scanner)
- netcat
- NFT (first IDS)
The idea of securing the system by trying to break them was initially not very well welcomed by the industry.
In 2000 companies starts to hire hackers.
2002 – Microsoft Trustworthy computing – all the process of this initiative have been influenced by hackers
2003 (modern security era)
- pen test became a requirement
- companies create bug bounty programs
The idea that the security is an external process that is applied at the end is broken.
The security must be embedded in each part of the SDLC.
See no evil, hear no evil: Hacking invisibly and silently with light and sound
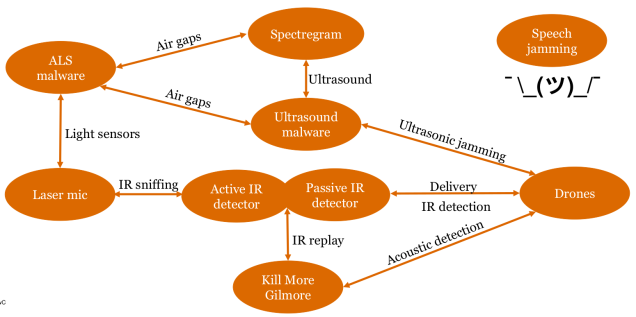
The talk was about how the sound and light can be used to remotely extract information and was articulated around 3 parts:
- jumping air-gaps
- air-gap = computer isolated from the network; the goal is to make jump the air gap between the computer and the network in order to get exfiltrate data from the network.
- ways of exfiltrate data from the network
- screen luminosity; used to sent commands to an infected laptop, or used for data exfiltration.
- near-ultrasonic sounds; same goals as the previous one
- spectregram – embed images in sound files.
- mitigation for jumping air-gaps
- screen filters
- disable luminosity sensors
- disable microphones/speakers
- surveillance and anti-surveillance
- laser microphone – quite easy and cheap to make
- sniffing and cloning the IR (infra-red) signals; used for bypassing the IR Motion detectors
- funny things (done by the presentr)
- Delayed Auditory Feedback (speech jamming) – the presenter build a software version.
- Demotivating malware analysts – create aspectregram and add it to a program that somebody will try to reverse it.
- ultrasonic attack against drones
This is kind of mind-map of the talk:
XFLTReaT: a new dimension in tunnelling
This talk have 2 goals; the fists one is about building tunnels and the second goal is to present the XFLTReaT framework. Apparently the framework is very modular and very easy extensible.
XFLTReaT
- tunneling framework
- plug and play
- modular
- you do not have to take care by yourself about:
- set up routing
- handle multiple users
- encryption
Client-Server approach; The client have a check functionality to find out which protocol is not filtered on the network.
You must be logged in to post a comment.